This post summarises the Winbox server vulnerability in RouterOS, discovered and fixed in RouterOS on April 23, 2018. Note that although Winbox was used as point of attack, the vulnerabilitty was in RouterOS. This issue was later assigned a universal identifier CVE-2018-14847.
How it works: The vulnerability allowed a special tool to connect to the Winbox port, and request the system user database file.
Versions affected:
- Affected all bugfix releases from 6.30.1 to 6.40.7, fixed in 6.40.8 on 2018-Apr-23
- Affected all current releases from 6.29 to 6.42, fixed in 6.42.1 on 2018-Apr-23
- Affected all RC releases from 6.29rc1 to 6.43rc3, fixed in 6.43rc4 on on 2018-Apr-23
Am I affected? Currently there is no sure way to see if you were affected. If your Winbox port is open to untrusted networks, assume that you are affected and upgrade + change password + add firewall according to our guidelines. Make sure that you change password after an upgrade. The log may show unsuccessful login attempt, followed by a succefful login attempt from unknown IP addresses.
What do do:
- Upgrade Winbox and RouterOS
2) Change your passwords.
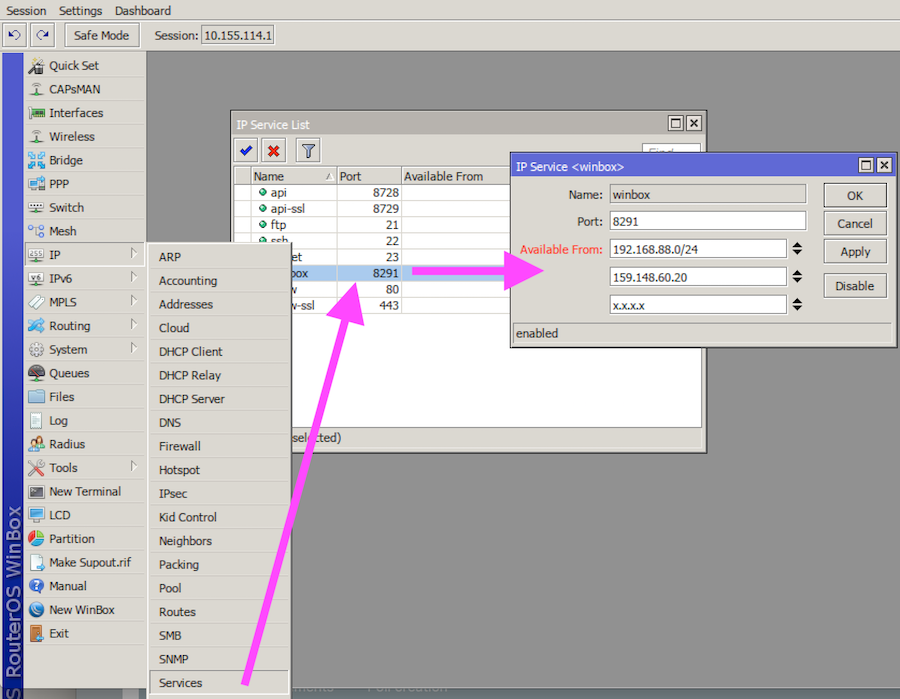
3) Firewall the Winbox port from the public interface, and from untrusted networks. It is best, if you only allow known IP addresses to connect to your router to any services, not just Winbox. We suggest this to become common practice. As an alternative, possibly easier, use the “IP -> Services” menu to specify “Allowed From” addresses. Include your LAN, and the public IP that you will be accessing the device from.
- Use “Export” command to see all your configuration and inspect for any abnormalities, such as unknown SOCKS proxy settings and scripts.
Contact us about vulnerabilities